CHAPTER 1: Page 4
Preperation: It's time to get busy

Bo knew that he needed hard and fast evidence that something was actually happening. The last thing he needed was to accuse someone of something only to find out that he was wrong knowing that just having video proof would not be enough. After all, someone parking close by you is certainly not a crime.
To Bo, this was going to be the fun part. To trap these bastards Bo knew that he needed to build a complete surveillance solution and this would require a fairly complex plan.
Bo likes plans.
Bo's plan was slowly unfolding in his mind. Step by step he thought through each part of the puzzle, after all this is what he did every day at work. Find a problem and come up with a solution and he was paid quite highly to do this every day for his entire career. He needed equipment as well and it had to be mobile. His first thought was to simply use another mobile phone. He had a few old android phones just laying around with cracked screens, that would make a good target. He did not really need the screen to work, he would simply root the phone and then connect to it using another device that was set up for monitoring. He began to make a checklist.
This meant a trip to the store and Bo likes to shop, especially when it comes to electronics.
The List
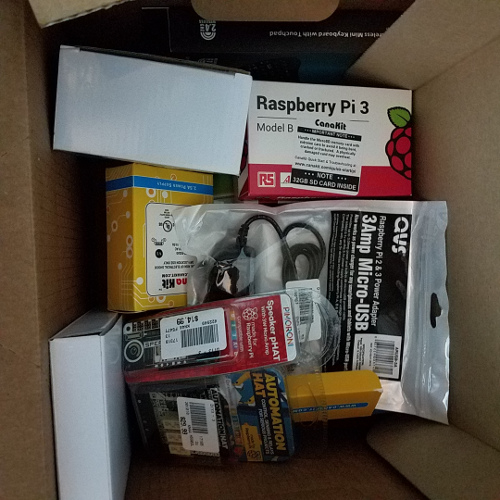
He decided to go with a few Pi's. They were small and did not consume much power and could be equipped with a plethora of add-on components. He would equip it with a small 5 or 7 inch touch display to make it easy to flip through screens and a controller for visible LED lights for alerting, after all Bo's eyes were not getting any younger. Bo was not quite sure how they were trying to access so he determined that his best route would be to set up the phone as a honey pot... a target. He would then monitor wifi traffic with the Pi and see what tries to connect. He had suspicions that the phones were being compromised by the Android OS location monitoring. If you think about it, it is really not that difficult. Any one of a million apps you could install on your mobile device can send your location back for targeting. Corporations use it all the time to monitor and track their employees. If someone had access or compromised that companies data they would have full access to all of their employees location. Any compromised app could simply feed your location back to a rogue server. You have seen it in the news, they have even tracked Fit Bit data to find locations on government employees at secret locations. It is an Internet of Things and any one of those things can be used for nefarious purposes, Bo was well aware of this... he had all of his equipment and now it was time to build... more fun.
- Log in to post comments